Configure Cisco Prime TACACS+ Authentication w/ ISE 2.4
If you’re using Cisco Identity Services Engine (ISE) 2.4 for your TACACS+ Authentication and you use Cisco Prime then you’ll be happy to know integrating the two is super simple.
If you followed my Cisco ISE TACACS+ guides then it’ll be even easier because my screenshots will be pretty close to what you’re running.
Related: Configure New Cisco ISE 2.4 Install for Use as TACACS+ Server
Adding Prime to Cisco ISE Network Resources
The first thing we need to do is add our Prime Server to Cisco ISE 2.4 as a network resource that we can match up to when authenticating.
- Navigate to Work Centers -> Device Administration -> Network Resources -> Network Devices and click Add

- Fill in the Name and enter the IP of your Prime server as you would any other network device. You can leave Device Profile to Cisco if unless you have reason to use otherwise.

- Check the box next to TACACS Authentication Settings to expand the options and fill in your shared secret. Click Save.

Configuring Cisco ISE TACACS Profile for Cisco Prime
Now we need to tell Cisco ISE how to interpret the data from Cisco Prime so that when we sign in we have the correct permissions. We will do this using a new TACACS Profile and updating our Authorization Policy.
- Navigate to Work Centers -> Device Administration -> Policy Elements -> Results -> TACACS Profiles and click on +Add.

- Give the Profile a Name (I’m using PRIME ALL) and click on Raw View.

- Now we need to head over to Cisco Prime to collect the data that we will paste into the Profile Attributes box under Raw View.
- Log into Prime, click on the Menu icon in the upper left corner of the screen, and navigate to Administration -> Users, Roles & AAA -> User Groups and then click on the Task List hyperlink next to the group that you want your account to be part of when authenticating through TACACS+. In my case I’m using Admin.

- Copy all of the contents of the Task List box.

- Paste the contents you just copied into Cisco ISE in the box under Raw View where we left off earlier at step 2.

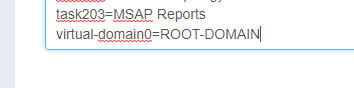
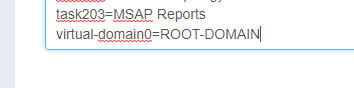
- Scroll to the bottom of the Raw View box and add a new line starting with virtual-domain0= as pictured below.
- Head back to Prime and Navigate to the Menu Icon -> Administration -> Users -> Virtual Domains and copy the name of the virtual domain you’re using. In my case it’s ROOT-DOMAIN.
- Go back to Cisco ISE to the Raw View box and add your virtual domain to the line starting with virtual-domain0= as pictured. In my case the final line in the Raw View box is now virtual-domain0=ROOT-DOMAIN.
- Click Save.
Configuring Cisco ISE Authorization Policy for Cisco Prime
Now we need to update your Authorization Policy.
- Go to Cisco ISE and navigate to Work Centers -> Device Administration -> Device Admin Policy Sets and click the right arrow to view your Policy. In my case I’m using the default policy.

- Expand Authorization Policy and click the Plus Icon to Add a new policy. Create a policy with your desired conditions using the Command Set Permit All and the Shell Profile (TACACS Profile) you created earlier using the Task List and Raw View box. You can see an example of my config here where if a npgdom.com domain user that is part of the Prime Admins group in AD signs into my Prime server at 10.2.2.2 they will be granted the unrestricted command set and PRIME ALL TACACS Profile based on the Admin group task list from Prime:

- Click Save when you’re finished.
Configuring Cisco Prime to Use TACACS+ Authentication
Now that Cisco ISE knows what to do with domain user’s that log into the Prime Server, we need to tell the Prime Server to use TACACS+ for it’s authentication.
- Go to Prime and navigate to Administration -> Users -> Users, Roles & AAA -> AAA Mode Settings and tick the radio button next to TACACS+ and check Enable fallback to Local.

- Choose which fallback method you want and click Save.
At this point you should be able to open a different browser or incognito window and log into your Prime server using your AD credentials (or whatever credentials you use with TACACS+ in your environment).


