Configure New Cisco ISE 2.4 Install for Use as TACACS+ Server
Now that we have functioning Cisco ISE (Identity Services Engine) 2.4 virtual appliance install, it’s time to configure it to act as a TACACS+ server.
The first thing I recommend anyone do with a new Cisco ISE install is disable the default password expiration setting. By default it’s set to 45 days. It’s no fun to wake up and find you’ve been locked out of your own ISE server and the steps to reset the password aren’t fun either.
- After logging into your Cisco ISE server navigate to Administration -> System -> Admin Access -> Password Policy -> Password Lifetime and uncheck the box next to Administrator passwords expire.

- Click Save.
Of course if you want to have the password expire, leave it checked and make sure to check the box to send an email reminder before it expires.
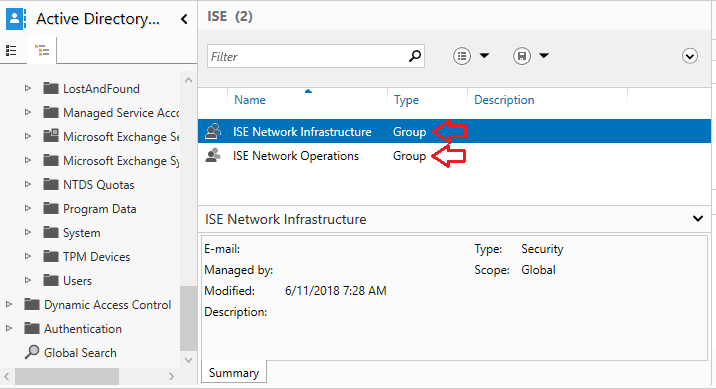
Create Active Directory Groups
To control the level of access users have when logging into networking equipment we need some groups created in Active Directory. For my setup I’m going to create two groups; ISE Network Infrastructure and ISE Network Operations.
In my environment the Infrastructure Team manages the networking equipment. The Operations Team mostly manages things at the server application level. It’s still handy for the Operations Team to be able to log into networking equipment and see how things are configured but we don’t want them making any changes.
The goal is to give the Infrastructure Team full access to networking equipment and limit the Operations Team to “show” commands.
Verify DNS is Configured
For ISE to work properly with AD you need to make sure that you set your domain name and DNS servers during the initial setup. You can verify these settings with the console (or SSH) command:
show run | include name

Join ISE to Active Directory Domain
The next thing we need to do is get ISE joined to the Active Directory Domain. This is what will allow ISE to match on the AD groups we created earlier.
- Navigate to Administration -> External Identity Sources -> Active Directory and click on Add.

- Enter your domain name in both the Join Point Name and Active Directory Domain boxes.
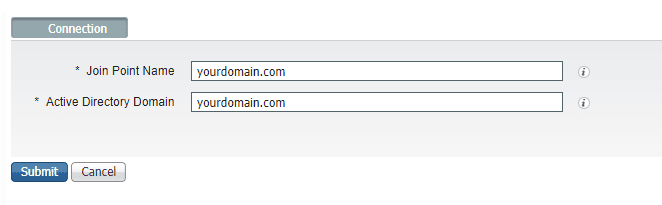
Join Point Name is essential a display name for your AD join. You can have multiple AD joins and the Join Point Name helps you tell them apart. In this setup we’re only using one domain so it doesn’t really matter.
- Click the Submit button.
- Click Yes to join all ISE nodes to this Active Directory domain when prompted.

Here is another “it doesn’t really matter” situation since we are only configuring one ISE node in this setup.
- Enter the credentials you use when joining machines to your domain.

You could also check the box to specify the organizational unit you want the ISE object to end up in. In my setup I’m not going to do this. I’ll simply move the object in AD if I decide I want it somewhere specific.
As for the “Store Credentials” box. You would use this if you wanted to save the credentials for joining other nodes. I don’t have any other nodes to join so I’m not going to check this box.
- Click OK.
You should now see the status of your Join Point change to Operational and list your domain controller.

Add Active Directory Groups to ISE
Now we are going to add the AD security groups we created earlier to ISE.
- At the same screen you were at to join AD, click the Groups Tab.

- Click Add -> Select Groups from Directory.

- Search for the groups you created and check the boxes in front of them.

In my case they were ISE Network Infrastructure and ISE Network Operations so I put “ISE*” in the Name Filter box to find only groups starting with ISE.
- Click Ok.
This next step is optional but I like to do it because it makes it easier to log into devices. You will be able to log into your networking devices without having to specify the entire FQDN.
- In the same window you were in to search the groups click the Advanced Settings tab and select the “Search in all the Whitelisted Domains” section” radio button.

- Click Save.
Create an Identity Source Sequence
The next step is to create and Identity Source Sequence. This will tell ISE what order of databases to search for a user account when authenticating to a device.
- Navigate to Administration -> Identity Management -> Identity Source Sequences -> New.
- Give you Identity Source Sequence a Name.
- Move your domain and the Internal Users group over to Selected from Available.
- Select the “Treat as if the user was not found” radio button.

The reason I choose the Treat as if the user was not found button is to allow using a local user created on the ISE server when active directory cannot be contacted. This prevents you from having to use the local account on the network device in cases where AD is unavailable. It’s not necessary but it’s another layer of protection.
- Click Submit.
Enabling TACACS
The first thing we need to do is make sure the Device Admin Services is running. To do this:
- Navigate to Administration -> System -> Deployment.
- Check the box next to your ISE server and click Edit.

- Check the box next to Enable Device Admin Service.

- Click Save.
Adding Devices to ISE
Now that we have enabled TACACS we need to add some network devices. It’s up to you how you want to add devices. You can add them by individually, by subnet, or set up a profile to match all devices.
I’m going to add my devices individually.
- Navigate to Work Centers -> Device Administration -> Network Resources -> Network Devices and click Add.

- Fill in the Name and IP.
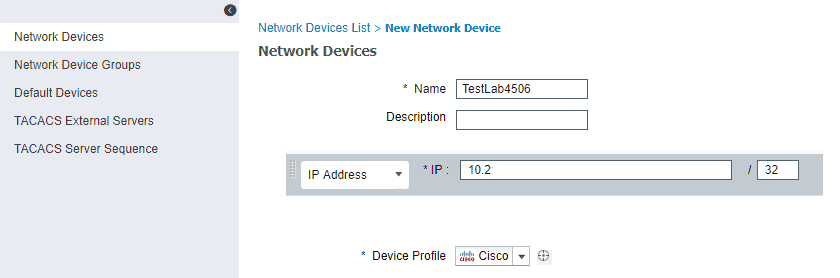
In my case I’m using a 4506 chassis switch with a sup8l-e supervisor card for testing so I’m going to leave the device profile as Cisco
- Check the box next to TACACS and enter the shared secret you wish to use with that device.

The checkbox for Enable Single Connect Mode is optional but it’s a good idea to use it if you have a stable network connection between your devices and the ISE server. What this setting does, in very basic terms, is keep a single tcp connection open between the device and the ISE server while authenticated to the device. Without this option the server will open a new connection for every subsequent TACACS+ request from the device. This means less network overhead and response times.
Configuring TACACS Command Sets
Now that we’ve added a network device we need to configure some command sets. Command Sets control what commands an authenticated user can enter into a network device.
I want to configure a set that allows my ISE Network Infrastructure group to have full access to all commands within a device and another set that only allows “show” commands for my ISE Network Operations group.
- Navigate to Work Centers -> Device Administration -> Policy Elements -> Results -> TACACS Command Sets and click Add.

- Type Permit All in the Name box and check the “Permit any command that is not listed below” box. Do not add anything to the list below that.

By not specifying anything in the list below this rule is basically saying allow all commands. This will be the command set used for the ISE Network Infrastructure group later.
- Add another policy set and name it Show Only. Then click Add and select Permit under Grant and type show* in the command box.

Within the Command box you can use * as a wild card. That means show* will allow any form of show command. If you want to limit the arguments after show you need to know that * is not a wildcard in that box. The arguments box uses REGEX so you would type .* for wild card statements. For example v.* would allow version and any other argument starting with a V.
- Click submit.
We should now have a total of 3 command sets, the default Deny All and our Permit All and Show Only sets.
Configuring TACACS Authentication Policy
Now we need to tell ISE what Identity Source Sequence to use and then define the Authentication Policies that will give our AD groups the right command sets.
- Navigate to Work Centers -> Device Administration -> Device Admin Policy Sets and click on the Default policy set.

This one is a little tricky. You have to click the right arrow (or sideways carrot) icon. Also, if you prefer, you can create a new policy set instead of editing the default. This is meant to be a simple TACACS setup so I opted to just make the changes to the default policy set.
- Click the down arrow (or upside down carrot) to expand Authentication Policy and change the Use box to the AD_Internal Identity Source Sequence we created earlier.

- Expand Authorization Policy and click the + icon.
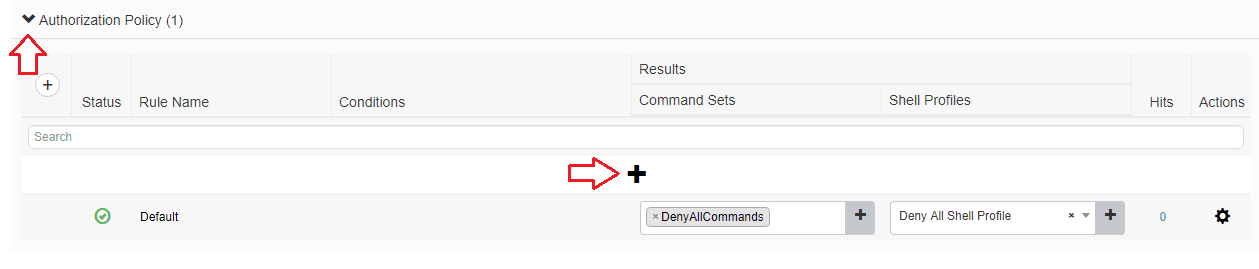
- Give your policy a name. In my case it’s Allow All Infrastructure Group. Set the command set to Permit All. Set the Shell Profile to Default Shell Profile (we aren’t going to worry about shell profiles for now). Then, click the + icon.

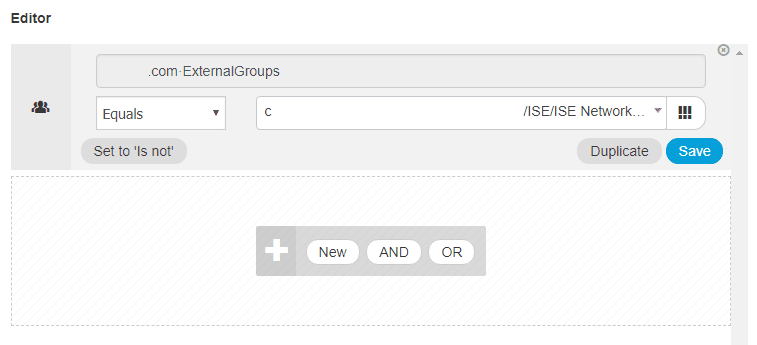
- In the editor that opens click into the Click to add an attribute box and select “Yourdomain.com External Groups” and then choose ISE Network Infrastructure from the List in the box to the right of Equals.
- Click Use.
- Repeat 3-6 for the Operations Group except change the command set to Show Only and give it a unique Rule Name.

- Click Save.
Configuring the Networking Equipment for TACACS+ through ISE
We’ve now configured ISE well enough to act as a basic TACACS+ server. Now we need to tell our networking equipment to look to the ISE server for authentication requests.
I’m going to assume that if you’re working with Cisco ISE then you know how to configure AAA on a Cisco device. I’m also going to assume that you already know how to enable and configure SSH on Cisco equipment. Because of that I’m not going to cover this in detail. What I will show are the settings I applied to get this working on my 4506.
aaa new-model
!
aaa group server tacacs+ default
server name TAC_ISE
!
aaa authentication login default local group tacacs+
aaa authentication login console local
aaa authentication enable default group tacacs+ enable
aaa authorization config-commands
aaa authorization exec default local group tacacs+
aaa authorization commands 15 default local group tacacs+
aaa accounting exec default start-stop group tacacs+
aaa accounting commands 1 default start-stop group tacacs+
aaa accounting commands 15 default start-stop group tacacs+
!
tacacs server TAC_ISE
address ipv4 X.X.X.X
key mysharedsecret
!
line con 0
privilege level 15
login authentication console
line vty 0 4
privilege level 15
transport input ssh
line vty 5 15
privilege level 15
transport input ssh
!
This configuration allows local authentication which falls back to tacacs+ if the credentials entered aren’t in the local database. It also requires local credentials at the console. I did this to allow using either local or tacacs+ credentials through SSH and local only at the console.
A more secure setup would be to have group tacacs+ first before local on the auth lines which would prevent use of a local account when your ISE server is online and would log all login attempts to the ISE server.
Checking the ISE Logs for TACACS Results
If you navigate to Operations -> TACACS -> Live Logs you can see your TACACS login events. In my case I am part of the Infrastructure group that has full access to the networking equipment. You can see in the below screenshot that I was successfully authenticated and Authorization Policy given to me was the Allow All Infrastructure.

When I submitted show run and conf t commands they worked properly.
I removed myself from the ISE Network Infrastructure Group and added myself to the ISE Network Operations group in AD and ISE reported appropriately.

When I tried to submit a conf t command my result was “Command authorization failed.” Success.
Finally I removed myself from the Operations group and made sure I wasn’t in the Infrastructure group and ISE properly rejected my authentication request to the switch.




Very useful , thanks for your time and work