Using RUNAS Command to Run as Another User
For security reasons, it’s important that you don’t use the same account for daily tasks (like logging into your workstation and work on documents and email) as you do for admin tasks (like managing accounts in Active Directory or administrating vSphere).
I’ve worked in many environments where the SysAdmins and Network Admins only had one account and it was part of the Domain Admins group in AD. This is a very bad idea. Those credentials get cached into workstations, mobile devices, email portals, etc… You’re essentially risking the keys to the kingdom for the sake of convenience.
In an ideal world administrators would have three sets of credentials. They would have their regular user accounts for logging into workstations, a user account for administrative tasks, and a just-in-time user account for performing high level AD tasks that is a member of the Domain Admins, Enterprise Admins, or Schema Admins while special tasks are being performed.
Microsoft refers to this as the Least-Privilege Administrative Model which you can read more about here.
One conundrum that comes up under this model is how to run your admin tools, such as Active Directory Administrative Center and other RSAT tools, as a privileged account. Let’s discuss a few easy options.
Using a Secure Workstation or Server as a Jump Host
The best option is to have a secure terminal that you can simply log into using your admin credentials. This could be a locked down workstation or server. Then you can install your admin tools and run them like normal. You should also have group policies in place controlling the caching and saving of credentials used when remoting into these machines.
An example of this in action would be:
- Deploy a secure server.
- Install your admin tools to this server.
- Deny open access to the internet from this server.
- Use multi-factor authentication to access this server.
- Lock down your management consoles to only accept connections from this server (such as vcenter web console, Cisco ISE web console, etc..)
Using the RUNAS Command with Command Prompt and PowerShell
If you don’t have the ability to run separate secure workstations then you can use commands to launch your tools as your privileged account. The simplest of which is the RUNAS command which is available on all Windows 10, Windows 11, and Windows Server OSs.
As an example, lets suppose you want to launch ADAC (Active Directory Administrative Center) as your privileged account. You could run the following command inside of an elevated command prompt window:
runas /netonly /user:rsanchez@npgdom.com “%windir%\system32\dsac.exe”
Or this command in an elevated PowerShell window:
runas /netonly /user:rsanchez@npgdom.com “$env:windir\system32\dsac.exe”
If you wanted to open the classic Active Directory Users & Computers (ADUC) as another user you could use the following command:
runas /netonly /user:rsanchez@npgdom.com "mmc %windir%\system32\dsa.msc"
Or the PowerShell equivalent:
runas /netonly /user:rsanchez@npgdom.com "mmc $env:windir\system32\dsa.msc"
Other popular management consoles that can be launched this way are:
RUNAS Group Policy Management Console
runas /netonly /user:rsanchez@npgdom.com “%windir%\system32\gpmc.exe”
RUNAS DNS
runas /netonly /user:rsanchez@npgdom.com “%windir%\system32\ dnsmgmt.msc”
RUNAS DHCP
runas /netonly /user:rsanchez@npgdom.com “%windir%\system32\ dhcpmgmt.msc”
RUNAS Active Directory Domains and Trusts
runas /netonly /user:rsanchez@npgdom.com “%windir%\system32\ domain.msc”
Script RUNAS
Admittedly, launching a command line window and typing out a command every time you want to launch a console is time consuming and annoying. One easy solution to this is to create a script that you can launch to run the command for you. To do this, create a text file with notepad and include your command prompt command from above. Then save the file with the .bat extension.

This creates a batch file that you can double click to launch your window asking for your credentials for that program.
Create RUNAS Shortcut
Another way to launch your console as another user is to create a shortcut. To do this just:
- Right click your desktop or file explorer window in an empty space and click on New -> Shortcut.
- In the “Type the location of the item” box, enter the same command from the first method above but begin it with the full path to the runas.exe like so:
C:\Windows\System32\runas.exe /netonly /user:rsanchez@npgdom.com “%windir%\system32\dsac.exe”

- Click Next.
- Enter a friendly name when prompted and click Finish.
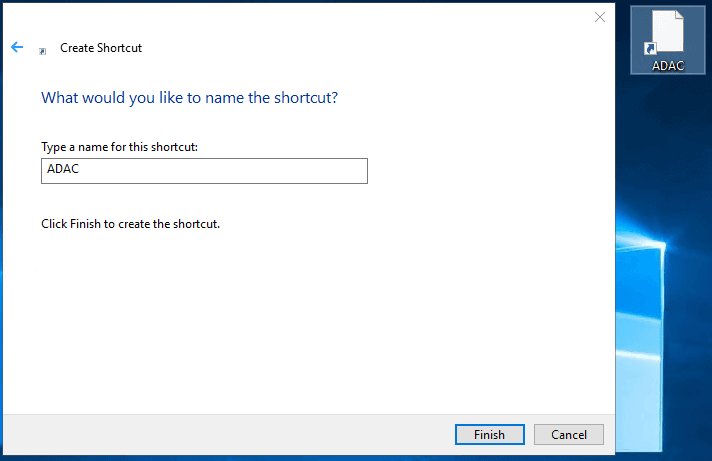
Now when you want to launch one of your programs as another you just double click the shortcut which will launch your prompt window asking for your password and subsequently launching your program.
As I mentioned earlier, the preferred method is to have a secure workstation or server that you log into with your admin account to perform your admin tasks. If at all possible, you should explore that option. I promise it’s not as intrusive as it sounds and will eventually become second nature for you. It’s a small price to pay for a huge slice of security.


