Using RSoP to Check & Troubleshoot Group Policy Settings
Resultant Set of Policy (RSoP) is a powerful tool built into Windows for auditing group policy settings. If you have never used this tool then you’re in the right place at the right time to learn!
As active directory domains grow so to does the amount and types of group policies. When creating new and editing existing policies you have all kinds of things you need to be aware of (or at least be able to test the outcome of) such as:
- Nested policies that conflict with eachother
- Loopback processing in play
- Item level targeting in play
- Order (and subsequently precedence) of GPOs
- Computer vs User Settings
- Permissions
- etc….
At one point in a time or another most of us will also inherit a domain that is rampant with group policies and we need a good way of evaluating how settings are being applied before and after we start making changes to clean things up.
That’s where RSoP.msc comes into play.
What is RSoP (Resultant Set of Policy)?
Simply put, RSoP is a built in tool shipped with all Windows 10, Windows 11, and Windows Server OSs that allows you to report on the group policy settings that have successfully applied to your user or computer account (or both).
You access the tool by running rsop.msc through the start menu, run program, or command prompt. The tool then opens a window that looks just like the GPMC (group policy management console) allowing you to navigate to all applied settings.
RSoP also has a planning mode that allows you to simulate the affects of policy settings. This mode is the is probably the least known part of RSoP and yet the most powerful for avoiding issues.
Explanation of RSoP Modes
As stated earlier, RSoP has multiple modes, logging and planning.
Logging Mode
This is the most commonly used mode. Logging Mode reports the settings that have successfully applied to the user and computer accounts.
Planning Mode
This is the last known and used mode, though it shouldn’t be! Planning mode simulates defined policy changes and reports the policy results. It’s like making a “what if” statement. For example, “What will happen if I enable loopback processing?” It’s really just a great way to save yourself (and you’re user’s) a lot of heartache.
How to Run and Use RSoP
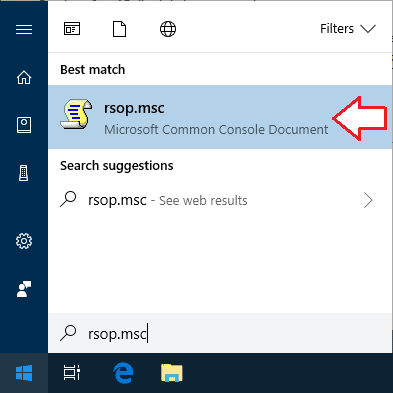
RSoP is a launched via a .msc file. This means you can open it through the start menu, run box, command prompt, or by navigating to the file within the Windows System Files. My preference is to just type it into the start menu (on Windows 10 and Windows Server 2019) like so:
- Type “rsop.msc” in the start menu and click on the icon that shows up (launching RSoP in Logging Mode by default):
- Wait for RSoP to process the polies:

- Navigate the Resultant Set of Policy window’s folder tree to review the policies that are applied to your machine:
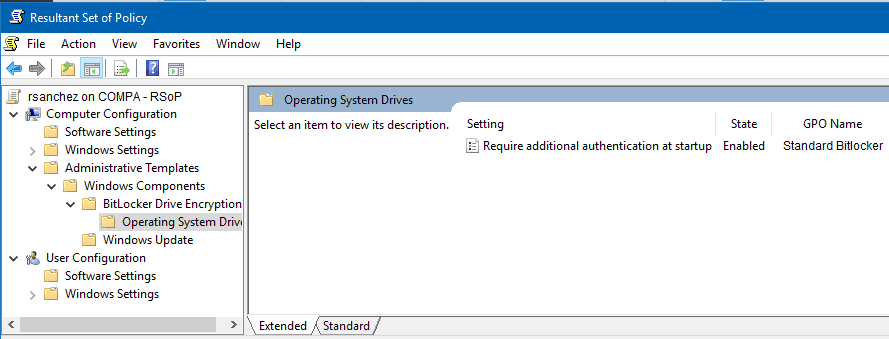
Looking through RSoP at the results we can deduce a number of things. First, we can see what settings are being applied to our machine. We can also see the name of policy that is causing that setting to apply (which means we know which policy is taking precedence or “winning” if we multiple conflicting policies). You can even right click on the policy setting and open a tab called Precedence that spell it out for you:

NOTE: I should mention that you need to be a local admin on the machine you’re running RSoP on if you want to see the computer results. If you’re just a standard user then you’re only going to see the user settings.
Now that you know how to log your group policy settings, let’s take it a step further and do some group policy setting simulation to plan out or policy deployment!
How to Use RSoP Planning Mode to Simulate Policy Settings
To simulate group policy changes and their affect on policy settings we need to make use of mmc.exe in conjunction with RSoP.
- Open mmc.exe by typing mmc.exe into the start menu and clicking on it (or your preferred method):

- Add the RSoP snap-in by navigating to File -> Add/Remove Snap-in… and then double clicking on Resultant Set of Policy to add it to selected snap-ins. Click ok.

- In the console window right click on Resultant Set of Policy and click on Generate RSoP data to open the RSoP Wizard. Click Next and select the radio button next to Planning mode. Click Next.

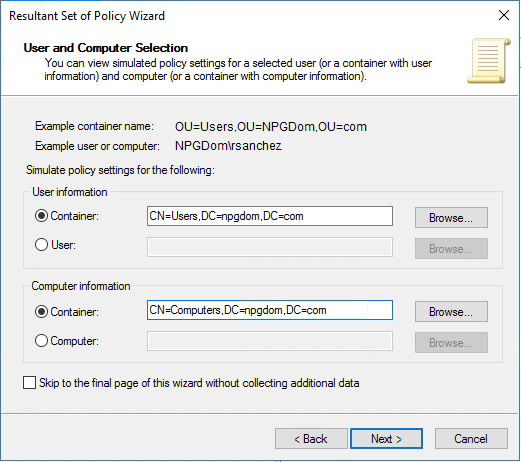
- Select the container or object that you wish to simulate with. In my case I’m going to simulate the affects of enabling Loopback processing so I’m going to select the user and computer containers that contain my affected objects. Click next.
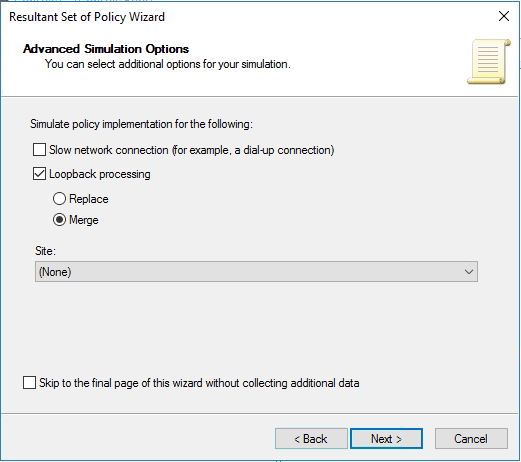
- The next screen I’m going to select Loopback processing and Merge since I want to see the affects when these settings are enabled within my containers.
- The next two screens allow you to simulate a change in security groups. For my simulation I’m going to leave these alone and keep clicking next.
- The next two screens let you simulate WMI Filter changes. I’m not using these options so I’m clicking next through them.
- Ahh, finally we are presented with our Summary of selections and can run the simulation. If everything looks good we can click Next.

- Wait while your simulation runs. Your progress bar should slowly fill up green (over several “Microsoft Minutes”)
Once your simulation has finished running you’ll be presented with the results in a similar window that of Logging Mode.
Navigate the tree just as you had in Logging Mode to see what your policy settings would look like if you made the proposed change (in my case enabled Loopback processing).
It may not seem like much since we didn’t choose a lot of options. However, that doesn’t mean that what we just wasn’t powerful. Rather than throw a Hail Mary and hope we don’t completely bork our domain and infuriate our users we were able to accurately predict the outcome of our proposed change and verify all will be good with the world.
Hopefully this short tutorial was valuable and saves you a lot of heartache in the future.



Great. Thanks!