How to Backup Cisco ISE 2.4
Performing a backup and establishing a backup schedule should be one of the first things you do with a new Cisco ISE (Identity Services Engine) install.
Before we can backup ISE we need to create a repository for ISE to write to.
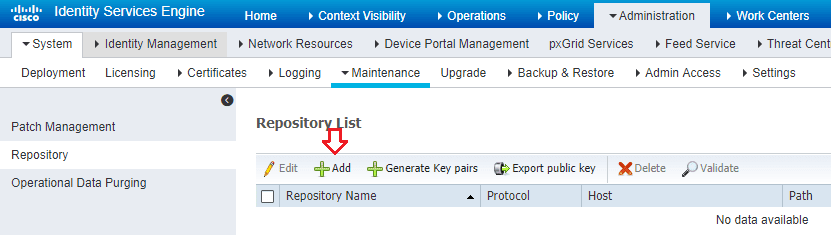
Creating a SFTP Repository within ISE
- Navigate to Administration -> System -> Maintenance -> Repository
This will bring you to the Repository List screen. We now need to add repository. In ISE 2.4 we can create many different types of repositories including DISK,FTP, SFTP,HTTP, HTTPS and so forth.
For this demonstration I’m going to use SFTP.
- Click the Add button
- Give your repository a name, choose SFTP from the protocol dropdown, type the IP address in the name box (or hostname if in DNS), and the path within your SFTP root directory. If you’re dumping your config right to your SFTP server’s root then you just need to put a /

After you click Submit you’ll receive the following prompt.

It sounds scary and complicated but it’s actually really simple.
We just need to log into the console of our ISE server (or SSH to it) and run the following command:
ISE/Admin# Crypto host_key add host X.X.X.X
Where X.X.X.X is the IP of your SFTP server.
One thing to note is that you enter this command at the enable prompt. You don’t run this from configuration prompt. It won’t work. That took me a while to figure out since it wasn’t that way in previous ISE versions.

With that out of the way we can now go back to ISE and set up a backup.
Backing up Cisco ISE
- Navigate to Administration -> System -> Backup & Restore
- Select the radio button next to Configuration Data Backup

- In the box that pops up enter a Backup Name, Select the Repository you created, and enter an encryption key.
The encryption key is something you specify so that your config backup is encrypted. This isn’t some key you can find somewhere in ISE. Also, to save you some heartache, there are some crazy requirements for the encryption key:
Encryption key must satisfy the following criteria:
* Contains at least one uppercase letter [A-Z].
* Contains at least one lowercase letter [a-z].
* Contains at least one digit [0-9].
* Contain only [A-Z][a-z][0-9]_#
* Has at least 8 characters.
* Has not more than 15 characters.
* Must not contain any of the characters ‘CcIiSsCco’
* Must not begin with #
Not allowing the letters in cisco to appear anywhere in the encryption key is a little annoying but I digress.
- Once you’ve conjured up an encryption key that satisfies all of these requirements, click Backup.

The backup process will begin. This would be a good time for a coffee break since it can take up to 10 minutes to perform the backup.
Perform these steps again for the operational backup. This one only takes couple minutes.
Backing Up ISE Certificates
You’ll notice when you run the configuration backup that ISE barks about needing to backup certs using the CLI. More specifically it says:
Internal CA Certificate Store in not in this backup. It is recommended to export it using “application configure ise” CLI command.
Fret not, this backup task is quite easy as well.
- SSH into your ISE server
- At the enable prompt (#) type:
ISE/admin# application configure ise
Select Configuration Option
ISE/admin# 7
Export Repository Name: yourrepositoryname
Enter encryption-key for export: yourencryptionkey
You should see a bunch of lines scroll and then end with “ISE CA keys export completed successfully”
At this point you can type 0 and press enter to exit. Then type exit again to close the SSH session.
Related: Cisco ISE 2.4 Certificate Install


